When we talk about IP-Routing we talk about forwarding packets to its destination based on different informations provided by the routing table (RIB). This table is composed of many things, but the most important is the destination and its next-hop. To know where the packet needs to be forwarded.
How is the information fed in the routing table?
There are three different sources where the information could come from.
Connected routes
These routes are networks configured on the interface of the device.
Static routes
This are manually configured routes that points to a specific network over a manually selected gateway.
Dynamic Routing protocols
Router has the ability to run specific protocols to exchange information between devices connected sharing the same segments. This protocols can forward information to its neighbors containing routes of devices that are not directly connected. Therefore the devices has a better connectivity by choosing a shorter path to a specific destination.
1.2.a Administrative distance
What happens if we received the same route we configured manually with the same prefix length coming from a dynamic routing protocol?
there is only space for one entry in the routing table for a network with same prefix length coming from different routing protocols. The decision is made first by the AD also called Administrative Distance. Every routing protocol has its own defined value for the administrative distance. For example, connected routes has an AD of 0, a static
route has an AD of 1 and OSPF has an AD of 110. The lower the value, the most preferred the route is.
Example:
If we configured manually a static route (AD: 10), telling the routing device that the network 192.168.1.0/24 is reached by the next-hop 10.10.10.2 and we receive the same network advertised by OSPF, a dynamic routing protocol (AD: 110), then the router will put the manually configured network in its routing table, since it has the lower AD.
What happens if we learn from two different OSPF neighbors the same network?
In this case both devices will have the same AD. Then in this case there is a further value called metric to be checked in order to choose the better entry.
What happens if they have the same metric?
This is an exception on my first statement above, that there is only one entry for a network with the same length.
If both have the same AD and same metric, then the router will put both destinations in its routing table, performing Equal Cost Multi-Path routing (ECMP).
Forwarding the packet
Once the routing table its fed with information, the router can make some decisions. Whenever a packet needs to be forwarded, the router will perform this task based on the routing table. The router will compare the L3 destination of the packet and compare it with the routing table entries. The longest match will win, this means
the more specific route is preferred.
Example:
The router needs to forward a packet to 10.10.10.7.
The routing table has three entries
a) 10.0.0.0/8 next-hop 192.168.1.2
b) 10.10.0.0/16 next-hop 172.23.255.2
c) 10.10.10.0/24 next-hop 10.13.13.2
The more specific entry is the route C and the packet will forwarded to the next-hop
10.13.13.2
Once the right next-hop is selected the router needs to understand over which interface the packet needs to leave (egress interface). The next-hop address will be compared with the connected, once the right one has been found the last step is to encapsulate the packet with a new L2-header with the destination MAC-Address of the next-hop. If the MAC-Address is not known an ARP-Request will be performed to gathered the needed information.
1.2.b VRF-lite
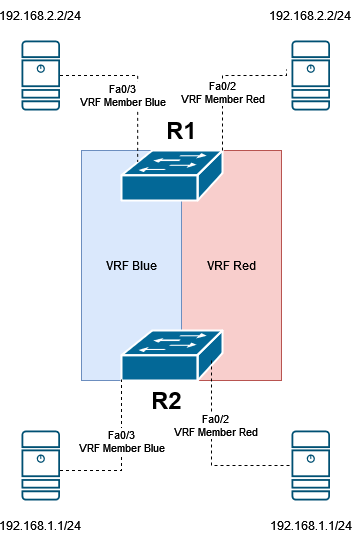
A router or routing device will use a routing table in order to make decisions. When we speak about VRF (Virtual Routing and Forwarding) we speak about creating multiple routing tables completly independent from each other. This could be clearly compared to the VLANs on Layer-2.
1.2.c Static routing
As mentioned above a static route is a manual way of selecting a next-hop for a network. Configuring static routes is a easier way of filling up the routing table in a small network where they are not so many routing devices.
There are different types of static routes:
Recursive Static Routes
This is the most common and simpliest way of static routes. Here just the next-hop for a network will be defined. The router will recursively look up in the table till finding the more specific entry matching the network. The way to configure it is the following:
(config)# ip route prefix mask next-hop address (config)# ip route 192.168.2.0 255.255.255.0 172.16.16.2
Fully Specified Static Routes
The same as the static route mentioned aboved, but we manually add the egress interface.
(config)# ip route prefix mask next-hop interface next-hop address (config)# ip route 192.168.2.0 255.255.255.0 Gig0/13 172.16.16.2
Floating Static Routes
For this type of route we additionally add a desired AD. Imagine that you receive an advertisement for the network 192.168.3.0/24 over OSPF, in case OSPF adjency for some reasons, like misconfiguration or process failure, looses his neighbor we can set a ‚backup‘ route with a higher Administrative Distance than OSPF (Higher than 110). As soon as the OSPF route is removed from the RIB, the floating static route will take its place till OSPF comes back again.
(config)# ip route prefix mask next-hop address AD (config)# ip route 192.168.2.0 255.255.255.0 172.16.16.2 111
Static Null Routes
The Null interface is used to black-hole traffic, since this interface has no forwarding capabilities it will only dropped traffic that is sent to it. This method is use in order to avoid routing loops.
1.2.d Policy Based Routing
Policy Based Routing or PBR is a mechanism that can make forward decisions, superseding the RIB, based on different manually configured criteria.
It works based on route-maps configured on the source ingress interface.
ip route 10.10.100.0 255.255.255.0 172.16.35.1 ! ip access-list extended PolicyBasedRouting permit ip host 192.168.1.100 host 10.10.100.100 ! route-map PolicyBasedRouting permit 10 match ip address PolicyBasedRouting set ip next-hop 172.16.23.1 ! interface Ethernet0/0 ip address 192.168.1.1 255.255.255.0 ip policy route-map PolicyBasedRouting
We can see from the configuration output above, that traffic to 10.10.100.0/24 is being sent by a static route to the next-hop 172.16.35.1. However we created a route-map matching an extended ACL that set the next-hop to 172.16.23.1. The PBR is only local significant and only valid for R1, R2 will forward the traffic to its directly connected network and R5 will answer using R3 as a gateway for 192.168.1.0/24.

1.2.e VRF-aware routing with any routing protocol
In order to be able to use routing protocols within a VRF, we need to define it while configuring it. This are some examples for the routing protocols from the CCIE Blueprint.
Static Route
ip route vrf <VRF Name> <prefix> <mask> <next-hop address>
EIGRP
router eigrp <AS-Number> address-family ipv4 vrf autonomous-system
OSPF
router ospf <Process ID> vrf <VRF Name>
BGP
router BGP <AS-Number> address-family ipv4 vrf
1.2.f Route filtering with any routing protocol
Filtering routes help us to avoid certain routes to be learned or advertise from or to other neighbors. Imagine a mid-range edge router in your company that establish a BGP-Session with the ISP and receives 700 000 ipv4 routes. The router will crash due lack of resources, this can be avoided by only allowing specific routes to be learned from the neighbor.
1.2.g Manual summarization with any routing protocol
Summarization is a way to simplify multiple routes in one single route. This method has some advantange and disadvantages.
Advantages:
Imagine you have 100 Entries for your campus network:
172.16.1.0/24
172.16.2.0/24
172.16.3.0/24
172.16.4.0/24
172.16.5.0/24
172.16.6.0/24
172.16.7.0/24
172.16.8.0/24
172.16.9.0/24
172.16.10.0/24
172.1611.0/24
…
…
172.16.97.0/24
172.16.98.0/24
172.16.99.0/24
172.16.100.0/24
All this entries could be summarized into 172.16.0.0/17. By summarizing it into one single route, we will save: space in memory (One entry vs 100 entries), CPU cycles by reducing the amount of routes to be checked. Also convergence time should be reduce, due the fact that there are less routes to be installed into the routing-table.
Disadvantages
Summarizing routes cand end up into sub optimal routing, due the fact that routers will choose the path with the longest prefix. Its possible that the router make a different decision based on a more specifc learned route from another device in the network.
1.2.h Redistribution between any pair of routing protocols
There are cases, as an example when two companies merge, where a router is placed between two different autonomous systems like OSPF and EIGRP. Then we need to exchange information between protocols. We can use, as mentioned on 1.2.j, a filter in order to only allow certain routes to be advertised or learned.
1.2.i Routing protocol authentication
By the implementation of authentication we can add additional security by only allowing certain devices with the same password or hash to form a neighborship. This prevent an attacker to join our network and easily exchange information or injecting wrong routes into/with the routers.
1.2.j Bidirectional Forwarding Detection
BFD is a mechanism to identify link failures much faster than the routing protocol it self can do. Routing protocols actually subscribe to BFD (If configured) in order to put the neighborship down in case of a loss of link, without waiting for dead timers to be reached.